Amazon Web Services has introduced VPC Encryption Controls, a new capability that allows organizations to enforce encryption in transit across Virtual Private Cloud (VPC) traffic. Instead of relying on developers or application teams to manually configure TLS or other encryption mechanisms, AWS now provides centralized controls to mandate that network traffic between services is encrypted.
This move enables security and compliance teams to define and enforce encryption policies at the infrastructure level, reducing the risk of misconfiguration, plaintext data exposure, and internal network attacks. The feature aligns with growing regulatory pressure and zero-trust security principles, where no network—internal or external—is assumed to be safe by default.
While encryption in transit has long been recommended, AWS’s decision to make it enforceable at the VPC layer represents a major evolution in how cloud security responsibilities are shared between providers and customers.
The Broader Context: Why This Matters Now
For years, cloud security relied heavily on best practices rather than guarantees. Encryption in transit was encouraged, documented, and audited—but rarely enforced at scale. This approach worked when cloud environments were smaller and simpler. It breaks down in today’s reality.
Modern cloud environments are:
Highly distributed
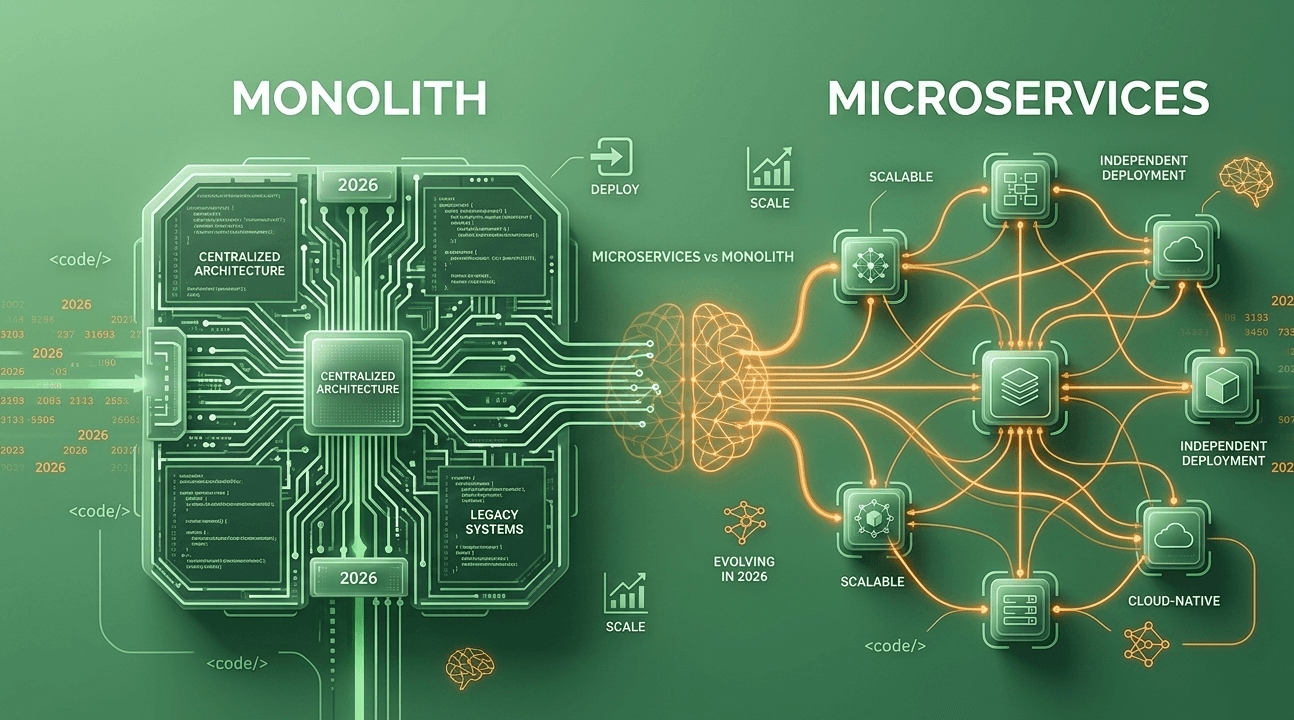
Built on microservices
Spanning multiple regions, accounts, and networks
Maintained by dozens or hundreds of teams
In such environments, human error becomes the dominant security risk.
At the same time, threat models have evolved. The assumption that traffic inside a VPC is inherently safe is no longer defensible. Lateral movement attacks, compromised credentials, misconfigured IAM roles, and insider threats all exploit implicit trust within internal networks.
AWS’s move reflects a broader industry realization:
Security controls must be enforced by infrastructure, not policies alone.
Historical Context: From Perimeter Security to Zero Trust
To appreciate the significance of VPC Encryption Controls, it helps to understand the evolution of cloud networking security.
Phase 1: Perimeter-Based Security
Early cloud security mirrored on-prem models:
Phase 2: Best-Practice Encryption
As breaches increased, providers encouraged:
However, adoption was inconsistent.
Phase 3: Zero Trust
The modern approach assumes:
AWS’s new controls represent a concrete step into Phase 3, where trust is removed by default and security is enforced by design.
What Makes AWS’s Approach Different
Infrastructure-Level Enforcement
Unlike application-layer encryption, VPC Encryption Controls operate at the network governance level. This means:
Developers cannot accidentally bypass encryption
Legacy services are covered
Security teams gain centralized visibility
Decoupling Security from Application Logic
This is critical. Many breaches happen not because encryption isn’t supported, but because it isn’t consistently implemented. By enforcing encryption outside application code, AWS reduces dependence on developer discipline.
Policy-Driven Security
Security becomes declarative:
This aligns with infrastructure-as-code and compliance automation trends.
Implications for Different User Segments
Large Enterprises
For regulated industries—finance, healthcare, government—this is transformative.
Enterprises can now demonstrate encryption guarantees without inspecting every application.
Security and Compliance Teams
This shifts power toward centralized governance:
Security teams gain leverage without slowing development.
Developers
The impact is mixed:
In practice, this improves overall quality but may initially frustrate teams used to flexibility.
Startups and SMBs
Smaller teams benefit from “secure by default” infrastructure, but may face:
Still, the long-term risk reduction outweighs short-term friction.
Comparison: How AWS Stacks Up Against Competitors
Google Cloud
Google has long emphasized encrypted-by-default networking, including automatic encryption of internal traffic. AWS is now closing a philosophical gap—moving from recommendation to enforcement.
Microsoft Azure
Azure offers encryption capabilities but often relies on customer configuration. AWS’s centralized VPC controls provide clearer guardrails.
On-Prem and Hybrid Solutions
Traditional data centers struggle to replicate this level of centralized enforcement without expensive tooling, highlighting the cloud’s growing security advantage.
Potential Problems and Criticisms
Performance Overhead
Encryption is not free. While modern hardware minimizes impact, high-throughput systems may experience latency or cost increases.
Legacy Compatibility
Older services or protocols may not support enforced encryption, creating migration challenges.
False Sense of Security
Encryption in transit does not solve:
Security remains multi-layered.
Operational Complexity
Policy enforcement introduces:
Strategic Commentary: Why AWS Is Doing This Now
This move reflects several strategic realities:
Regulatory Pressure Is Increasing
Governments are demanding demonstrable, enforceable security—not best-effort claims.
AWS Is Protecting Its Shared Responsibility Model
By offering enforcement tools, AWS reduces customer misconfiguration risk that often reflects poorly on the platform.
Security Is a Competitive Differentiator
As cloud services commoditize, trust and security become key selling points.
The Cloud Is Becoming the Default, Not the Exception
Security expectations for cloud infrastructure now exceed those of on-prem environments.
What This Means for the Cloud Industry
From Optional to Mandatory Security
We are witnessing a shift where:
More Opinionated Cloud Platforms
AWS is increasingly willing to impose guardrails, even if it limits flexibility.
Rising Bar for “Cloud-Native”
Applications that assume plaintext internal traffic will be considered outdated.
Predictions: What Comes Next
Encryption-by-Default Expansion
Expect AWS to extend enforcement to:
Cross-account traffic
Hybrid connections
Service-to-service APIs
Deeper Integration with IAM and Identity
Encryption controls will likely tie into:
More Automated Compliance Reporting
AWS will package these controls into audit-ready dashboards.
Industry-Wide Imitation
Competitors will follow, making enforced encryption a baseline expectation.
Expert Perspective: A Necessary, Not Optional, Evolution
From a security architecture standpoint, AWS’s move is overdue—but essential.
The cloud has reached a scale where trust-by-convention no longer works. Enforcement is the only sustainable model. By embedding encryption controls into VPC governance, AWS acknowledges that the weakest link in cloud security is not cryptography—it’s consistency.
This is not about protecting against elite hackers. It’s about eliminating everyday mistakes before they become incidents.
Final Analysis: A Quiet but Pivotal Shift
AWS VPC Encryption Controls will not generate flashy headlines. There are no user-facing features, no dramatic UI changes, no viral demos.
But make no mistake: this is one of the most consequential cloud security updates in years.
It marks:
The normalization of zero-trust networking
The decline of implicit internal trust
The rise of enforced security defaults
In the long run, this move will reduce breaches, simplify compliance, and reshape how cloud networks are designed.
For AWS customers—and the cloud industry as a whole—encryption in transit is no longer a recommendation. It’s the rule.